Intelligent and Automated Security Budget Optimization
Maximize your security program spend with automated measuring and reporting and prioritize investments based on actionable intelligence and reliable data.
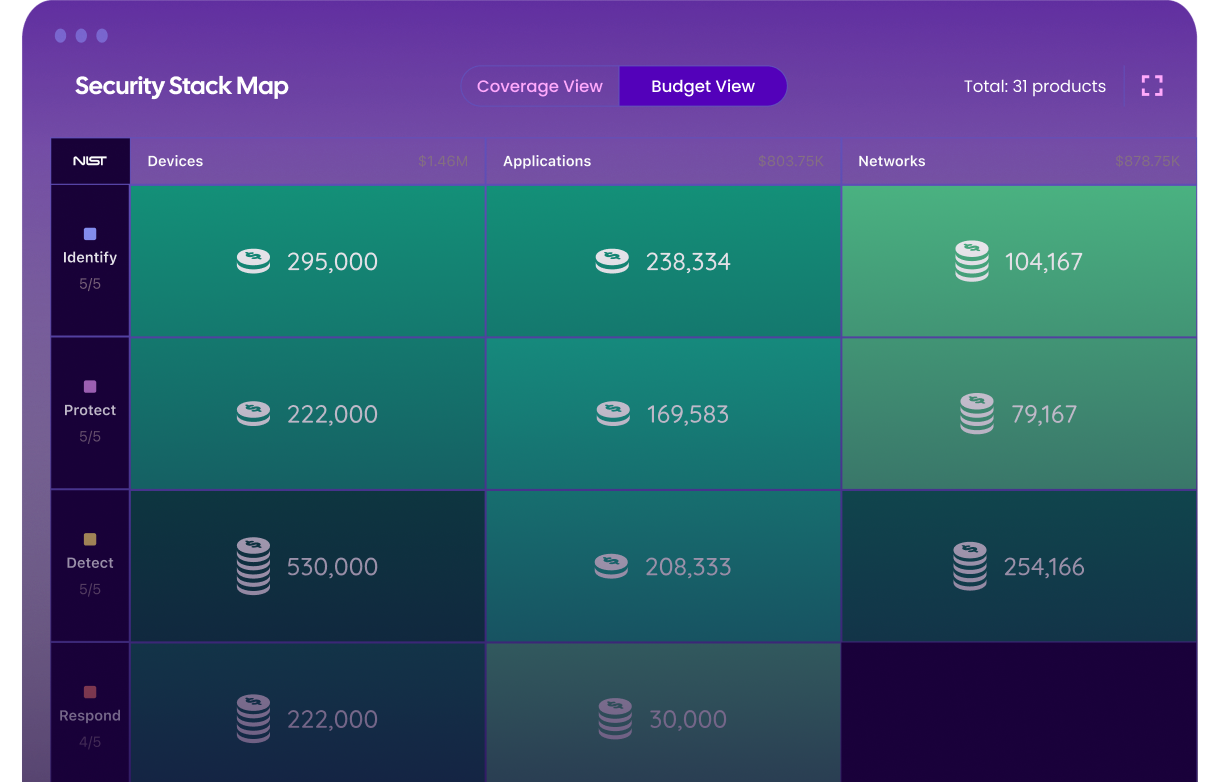
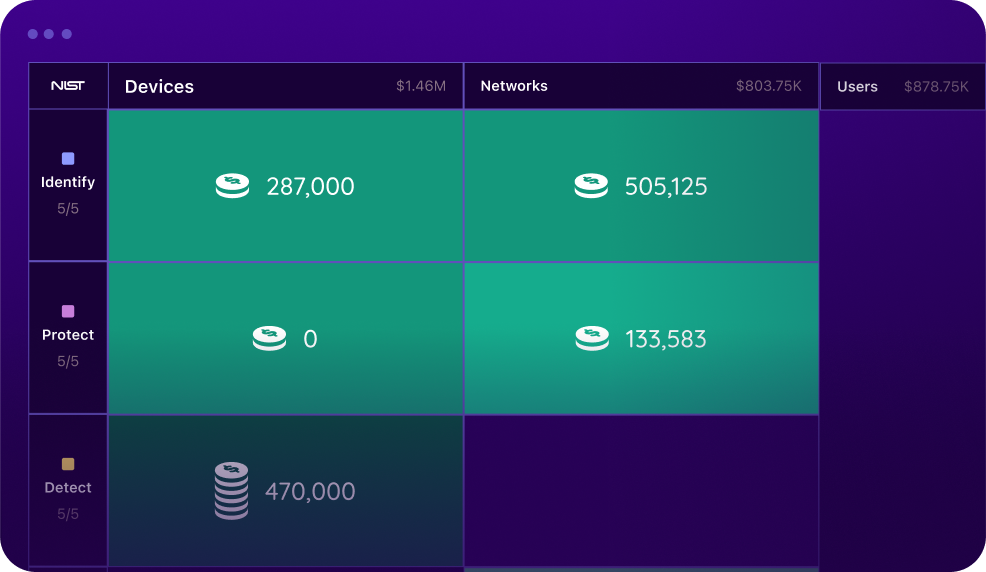
Onyxia enables you to gain a clear picture of how you are allocating your budget. Measure ROI based on product performance and utilization and review program spend in one place.
Evaluate, Measure, and Optimize Your Program Budget
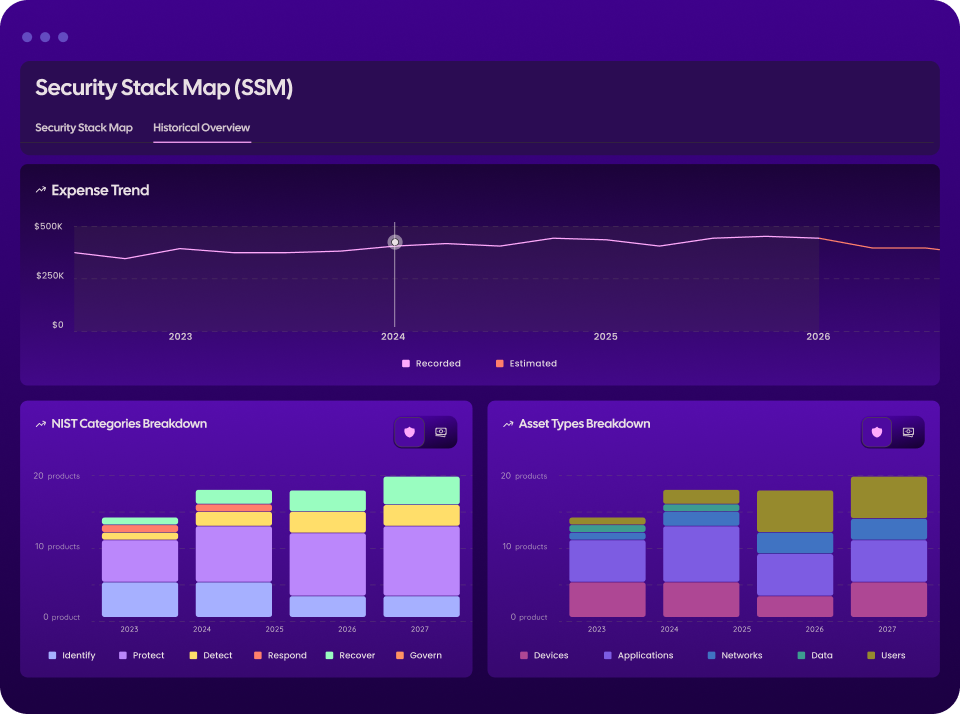
Make Smarter Resource Decisions with the Multi-Year Security Stack Map
Manage your security stack with historical context to better understand how investments have evolved, track spending trends, and forecast future budget requirements.

Easily Quantify And Demonstrate Your Security Strategy Effectiveness
Cyber risks can have immeasurable consequences for a business. Easily report on and highlight the value of your past investments in relation to avoided threats and attacks.
Why ROI and Cost Optimization Matters
Achieve Security
Strategy Goals
Ensure your budget can support the achievement of your most important security goals and metrics.
Strengthen Your
Program Performance
Wisely investing your budget in the right tech stack can help you avoid and combat emerging threats.
Convey Business Value
Ensure your budget can support the achievement of your most important security goals and metrics.

